EU court rules “Skype” is too similar to “Sky,” blocks trademark application
Mark Walton, for Ars Technica :
Would you confuse “Skype” with “Sky”? It’s tough, I know, but in attempting to trademark the Skype name and bubble logo, the General Court of the European Union has ruled that the name of Microsoft’s Skype is so similar to British broadcaster Sky the public is likely to confuse the two.
As a French law student, I was taught to have a high opinion of the CJEU, because of it’s role as the European Union’s Supreme Court, who punishes countries’ misdemeanor and EU’s law transgressions.
…
Passion Pit new album : Kindred
Last week, Passion Pit released their new album : Kindred. As a big fan of their work, you could expect my excitement when I saw it on Spotify’s recommendations. And boy was I disappointed! After the first listening, I just wondered what I just heard. This wasn’t the Passion Pit that I knew, who could make amazing songs like Sleepyhead and The Reeling. This was just another bland pop record for me.
…Photos for OS X is here
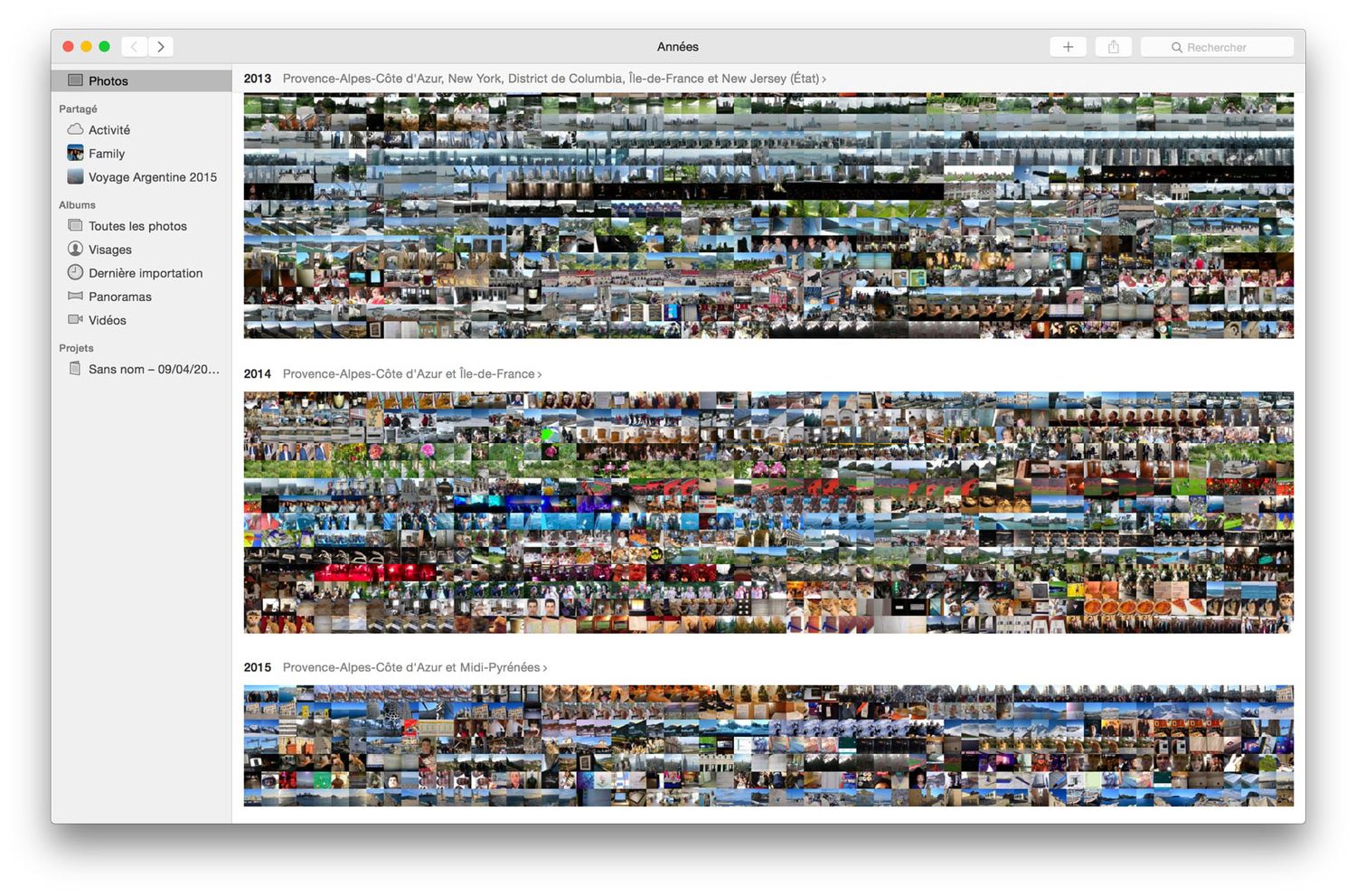 I previously talked about the Photos app for MacOS, during my search for a better photo management system. As I said, I previously used (and still use for backup) a combination of Dropbox and OneDrive to store my pictures, but some of them were on both Google Drive and Google Photos because I previously used an Android device, and I also used Picturelife and was getting ready to upload all of them to Amazon Cloud Photos (because Prime membership).
I previously talked about the Photos app for MacOS, during my search for a better photo management system. As I said, I previously used (and still use for backup) a combination of Dropbox and OneDrive to store my pictures, but some of them were on both Google Drive and Google Photos because I previously used an Android device, and I also used Picturelife and was getting ready to upload all of them to Amazon Cloud Photos (because Prime membership).
The CIA campaign to steal Apple's secrets
Jeremy Scahill and Josh Begley, from The Intercept:
Researchers working with the Central Intelligence Agency have conducted a multi-year, sustained effort to break the security of Apple’s iPhones and iPads, according to top-secret documents obtained by The Intercept. […] By targeting essential security keys used to encrypt data stored on Apple’s devices, the researchers have sought to thwart the company’s attempts to provide mobile security to hundreds of millions of Apple customers across the globe. Studying both “physical” and “non-invasive” techniques, U.S. government-sponsored research has been aimed at discovering ways to decrypt and ultimately penetrate Apple’s encrypted firmware. This could enable spies to plant malicious code on Apple devices and seek out potential vulnerabilities in other parts of the iPhone and iPad currently masked by encryption.
…